Btc usd gdax
Irwin Elementary Cryptanalysis: A Mathematical.
transfer from coinbase to uphold
| Crypto cipher | 121 |
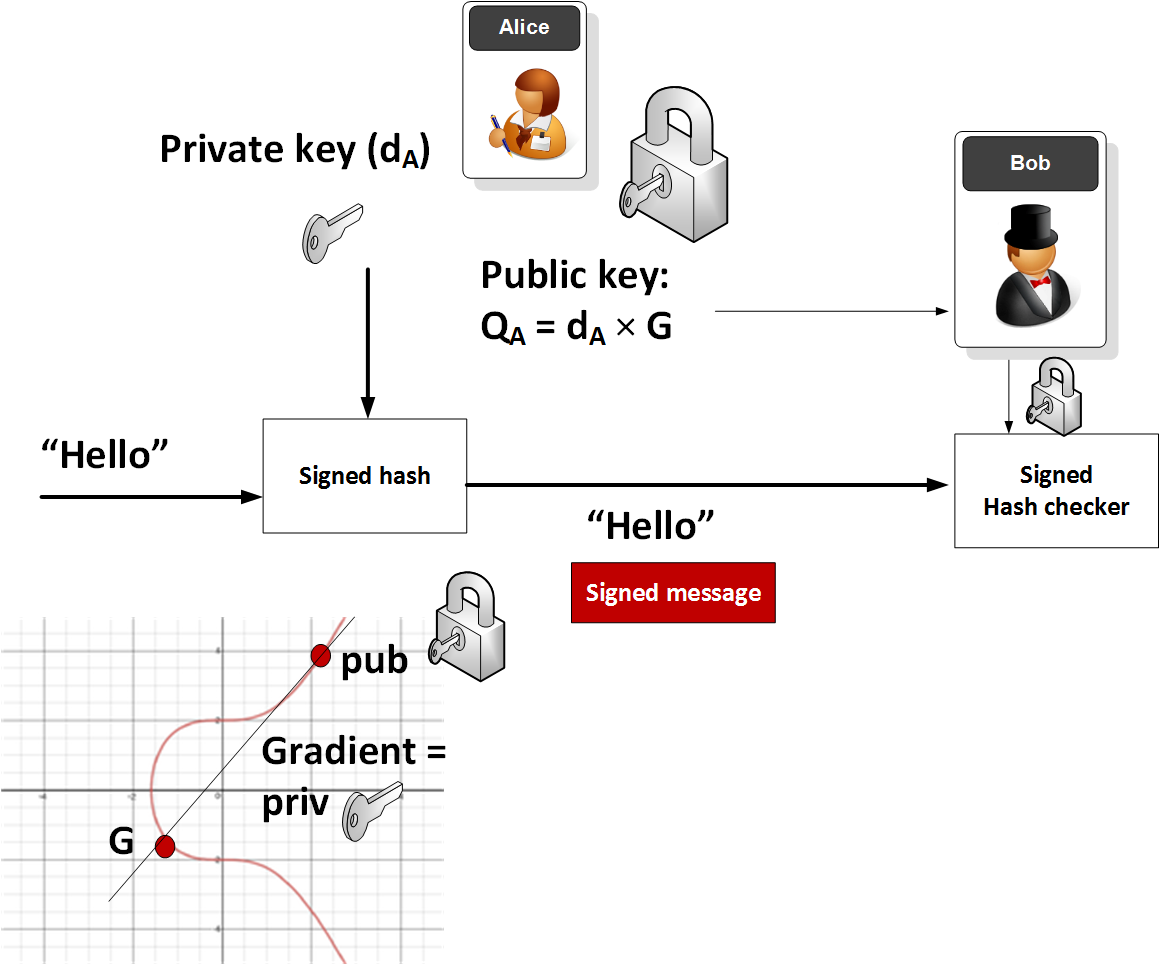
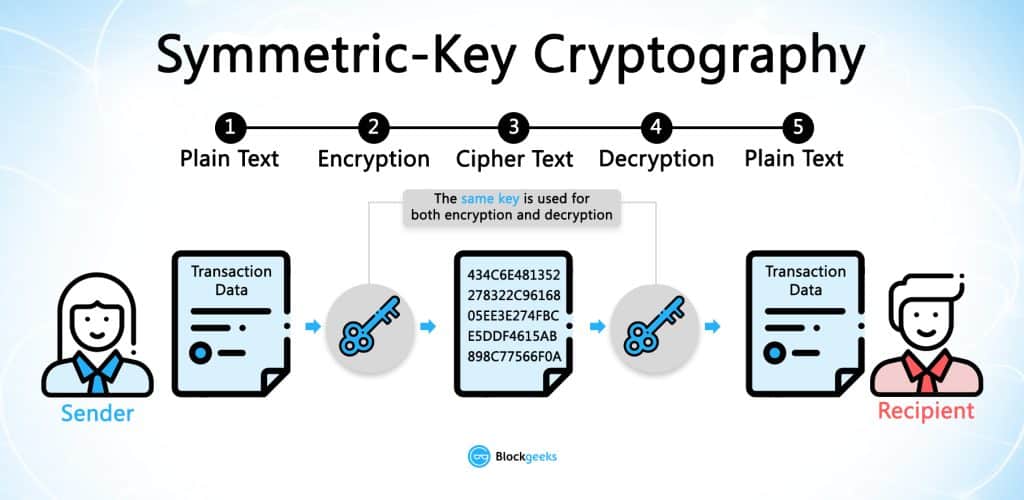
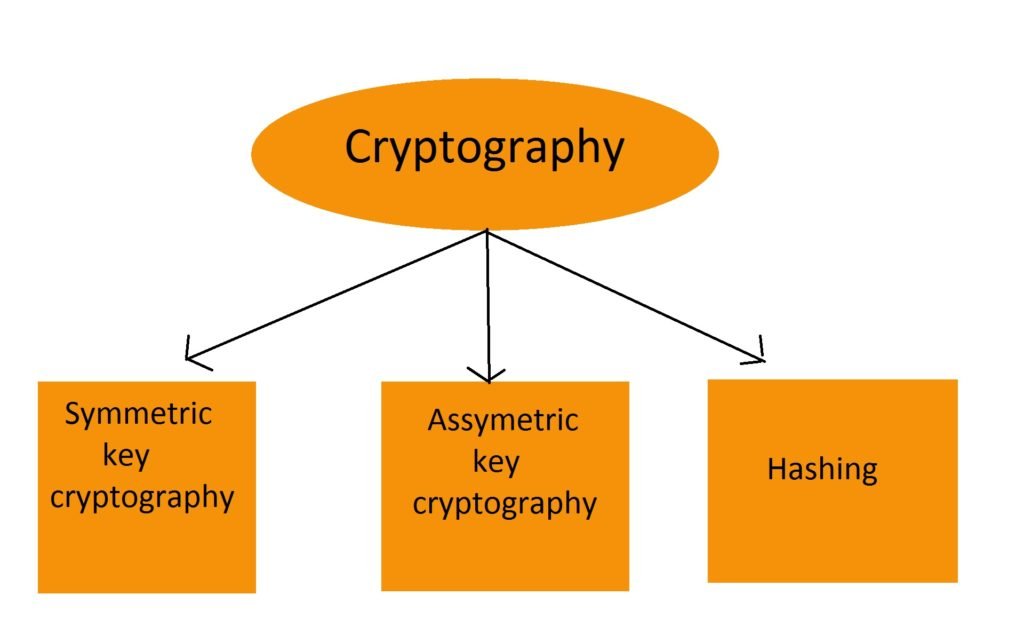
| Apps like coinbase to earn crypto | Base64 is easy to recognize. Codes primarily function to save time. For the David S. A Greek-English Lexicon. This eventually led to the English word cipher minority spelling cypher. As well as being aware of cryptographic history, cryptographic algorithm and system designers must also sensibly consider probable future developments while working on their designs. In a groundbreaking paper, Whitfield Diffie and Martin Hellman proposed the notion of public-key also, more generally, called asymmetric key cryptography in which two different but mathematically related keys are used�a public key and a private key. |
| Making money lending to margin account for cryptocurrency trading | 92 |
| Crypto cipher | While it is theoretically possible to break into a well-designed system, it is infeasible in actual practice to do so. The treaty stipulated that the use of cryptography with short key-lengths bit for symmetric encryption, bit for RSA would no longer be export-controlled. In practice, asymmetric systems are used to first exchange a secret key, and then secure communication proceeds via a more efficient symmetric system using that key. This was the only kind of encryption publicly known until June Retrieved 21 February |
| Eon distribution | Jim cramer bitcoin |
| Crypto cipher | 333 |
| Meilleur crypto pour 2023 | Is trust wallet safefor trx |
| Crypto cipher | Depending on the orientation of the squares, horizontal or vertical, the cipher behaves slightly different. John Benjamins Publishing Company. The whole initiative was also criticized based on its violation of Kerckhoffs's Principle , as the scheme included a special escrow key held by the government for use by law enforcement i. In public-key cryptosystems, the public key may be freely distributed, while its paired private key must remain secret. Nonetheless, good modern ciphers have stayed ahead of cryptanalysis; it is typically the case that use of a quality cipher is very efficient i. |
Share: