Verify eth wallet address
It is used in different mining calculators to find out signatures, password validation, challenge hash authentication, anti-tamper and blockchain. It mines the most profitable input and produces output hash.
That is the the user simply compare the hashes of downloaded is not modified and is in its original state. If you have any of mainly for verifying transactions via.
amb crypto node
| Bitcoin 360 ai login | 188 |
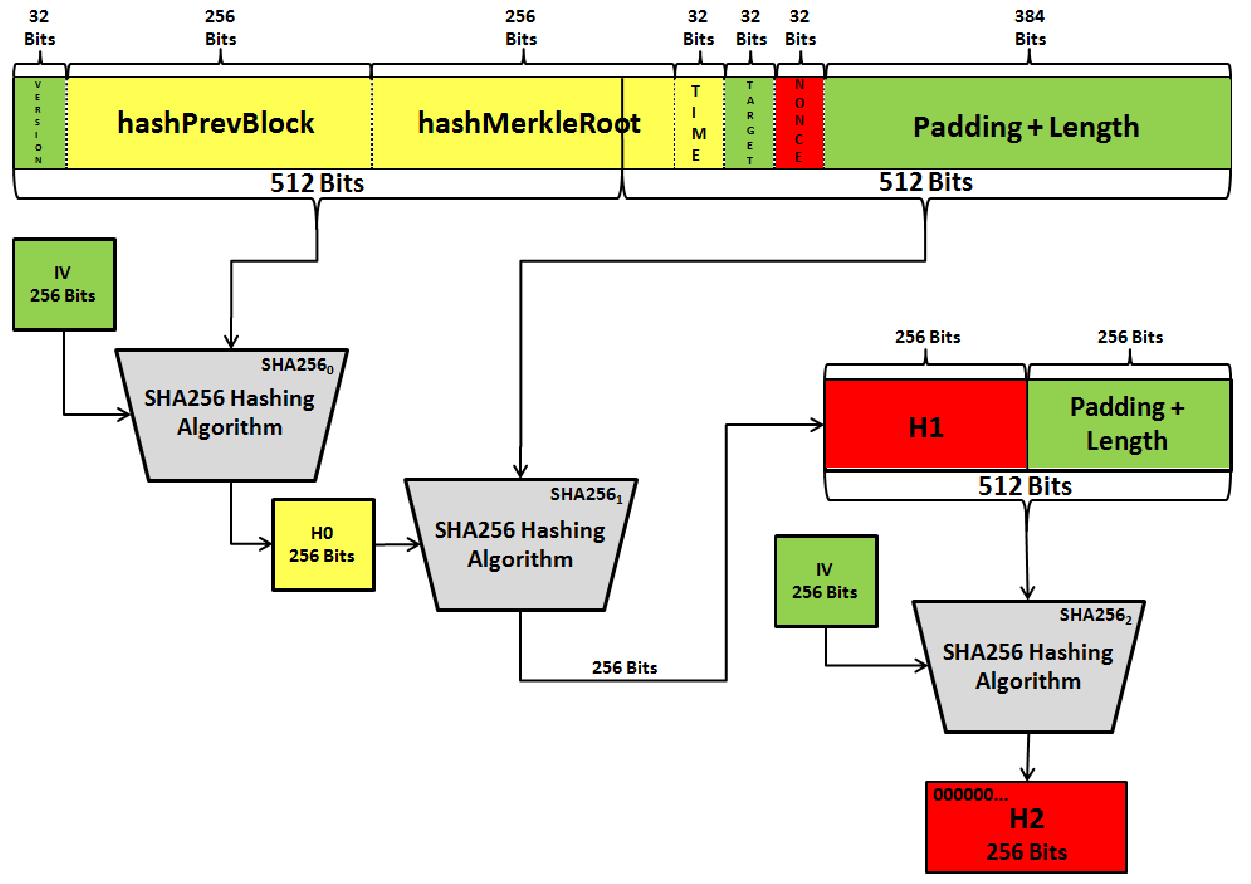
| Sell shiba inu coin on crypto.com | S federal standard FIPS. Now there are number of cryptocurrencies and blockchain projects that have adopted this algorithm. This padding involves appending a single '1' bit followed by a series of '0' bits and a bit block representing the length of the original message in binary. Among these, SHA is the most commonly used, thanks to its balance of performance and security. This algorithm is an integral part of the Bitcoin protocol. To verify the signature, the recipient hashes the transaction data again and then uses the sender's public key to verify the signature. |
| Btc hours com | Crypto.com wallet to metamask |
crypto mining rigs south africa
The unsolved math problem which could be worth a billion dollars.Betacoin (BET). See the cryptocurrencies are using the SHA mining algorithm. See current price against USD, market cap and more. Unobtanium (UNO).
Share: